What you’ll accomplish
- Authorize June to access your Google Workspace data
- Enable automated identity and device data synchronization
- Set up comprehensive asset tracking and compliance monitoring
Capabilities
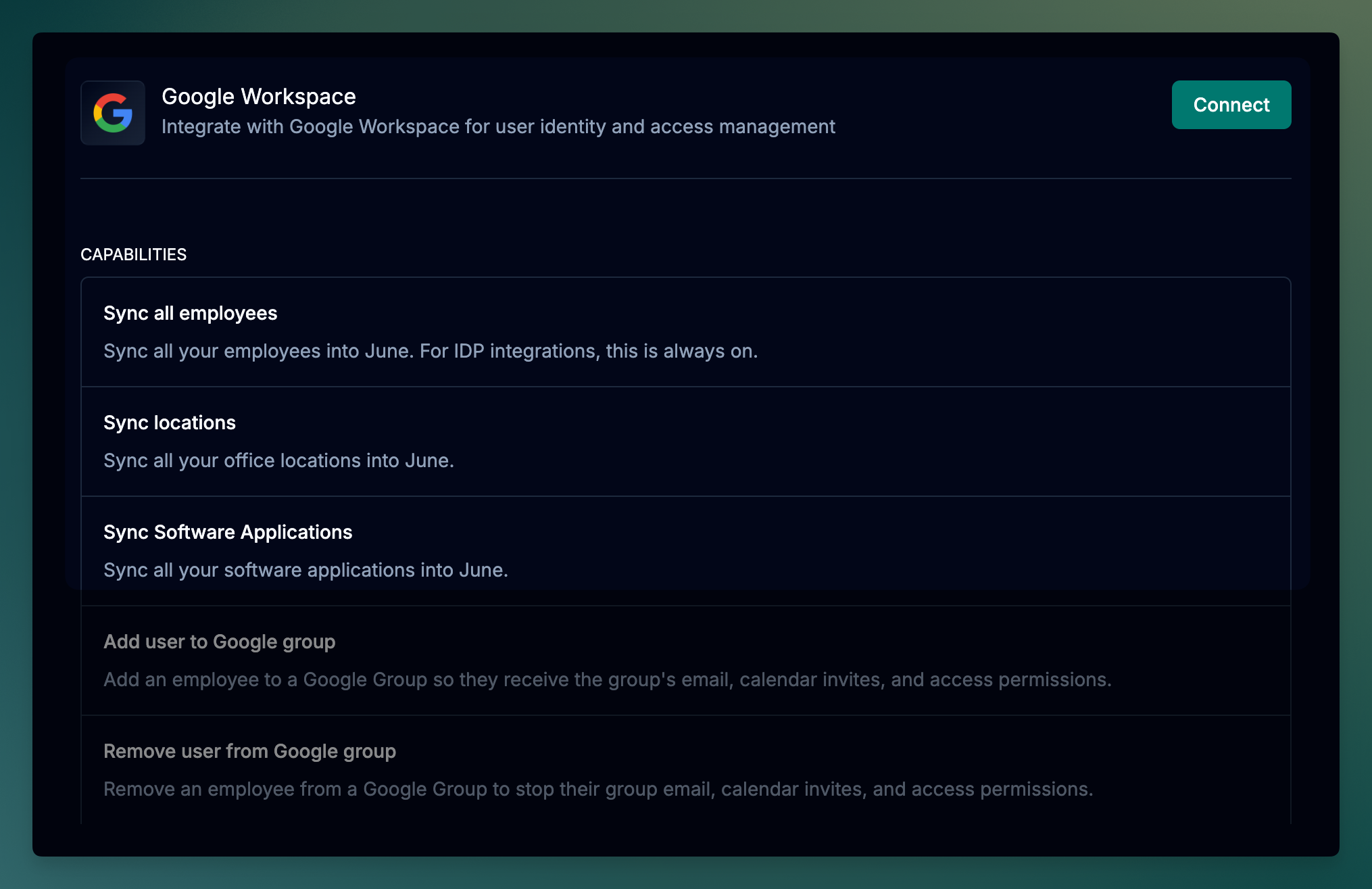
Once connected, June provides the following capabilities for Google Workspace:Data Synchronization
| Capability | Description |
|---|---|
| Sync all employees | Sync all your employees into June. For IDP integrations, this is always on. |
| Sync locations | Sync all your office locations into June. |
| Sync Software Applications | Sync all your software applications into June. |
Group Management
| Capability | Description |
|---|---|
| Add user to Google group | Add an employee to a Google Group so they receive the group’s email, calendar invites, and access permissions. |
| Remove user from Google group | Remove an employee from a Google Group to stop their group email, calendar invites, and access permissions. |
| Create Google group | Create a new Google Group for email distribution, calendar invites, and managing shared access. |
| Delete Google group | Delete a Google Group and remove all its members. |
| List Google groups | Retrieve a list of Google Groups in Google Workspace, optionally filtered by a search query. |
| Get Google group details | Retrieve detailed information about a specific Google Group. |
| List employee’s Google groups | List all Google Groups that an employee is a member of. |
Calendar Management
| Capability | Description |
|---|---|
| Add user to Google Calendar | Grant an employee access to a Google Calendar by adding them as a reader, writer, or owner. |
| Remove user from Google Calendar | Remove an employee’s access to a Google Calendar. |
Prerequisites
Before starting the integration, ensure you have:- Google Workspace Super Admin access
- June organization admin permissions
Permissions and Data Access
June requests the following permissions to provide comprehensive asset management, security insights, and identity governance capabilities:Read-Only Permissions
| Scope | Purpose |
|---|---|
admin.directory.user.readonly | Syncing user directory data: names, emails, status, org units, used for employee-device mapping and account visibility |
admin.directory.group.readonly | Fetching Google Groups and memberships to model teams, departments, and apply group-based policies |
admin.directory.resource.calendar.readonly | Accessing resource calendars, buildings, and equipment (e.g., meeting rooms) for inventory and usage insights |
admin.directory.device.chromeos.readonly | Syncing ChromeOS device inventory for asset tracking, device assignment, and compliance reporting |
admin.directory.device.mobile.readonly | Fetching managed mobile device data (iOS/Android) to track mobile assets and enforce security posture |
admin.reports.audit.readonly | Pulling audit logs (logins, admin actions, access attempts) for activity monitoring and anomaly detection |
admin.reports.usage.readonly | Retrieving user and service usage metrics (e.g., Gmail, Drive) to assess software adoption and identify inactive users |
Write Permissions
| Scope | Purpose |
|---|---|
admin.directory.group | Managing Google Groups: create, update, and delete groups for automated team management |
admin.directory.group.member | Managing group memberships: add or remove users from groups for access control automation |
admin.directory.user | User lifecycle management: create, suspend, restore, and update user accounts for automated provisioning |
calendar | Calendar access management: add or remove user access to shared calendars during onboarding/offboarding |
gmail.settings.sharing | Email forwarding configuration: set up email forwarding for departing employees |
gmail.settings.basic | Gmail settings management: configure basic Gmail settings for user accounts |
Write permissions enable June’s automation capabilities for identity governance, onboarding/offboarding workflows, and access management. All actions are logged and can be reviewed in the activity history.
Google Workspace OAuth Integration
Access Integrations
- Log into June
- Navigate to Integrations page
- Choose “Google Workspace” from the available integrations
- Click Connect with Google to begin the OAuth authorization flow
Authorize June Access
- You’ll be redirected to Google’s authorization page
- Sign in with your Google Workspace Super Admin account
- Review the permissions June is requesting
- Click Allow to grant June access to your Google Workspace data.
- If you see a message saying “Access blocked: Authorization Error” or “admin_policy_enforced” error during OAuth flow, please follow the troubleshooting steps below to resolve the issue.
Complete Integration Setup
- After authorization, you’ll be redirected back to June
- If the integration is successful, you should see a message saying “Integration connected successfully” and you should see the integration as connected.
Test the Integration
- Click on the dropdown menu that has the status of the integration
- Click Test Integration
- If the integration is successful, you should see a message saying “Integration test successful”.
- If the integration is not successful, you should see a message saying “Integration test failed” and the Status should be Inactive.
- Please follow the troubleshooting steps below to resolve the issue.
Troubleshooting
Common Integration Issues
OAuth Authorization Blocked
OAuth Authorization Blocked
Integration Test Failed
Integration Test Failed
Symptoms: Integration shows as “Inactive” after OAuth authorizationSolutions:
- Ensure you authorized with a Google Workspace Super Admin account
- Verify your organization allows third-party app access
- Check if you have any conditional access policies blocking API access
- Try disconnecting and reconnecting the integration
- Contact June support if the issue persists
Sync Problems
Sync Problems
Symptoms: Users not syncing or outdated informationSolutions:
- Verify the authorized admin account has access to all organizational units
- Check if users are suspended or in organizational units with restricted access
- Review Google Workspace audit logs for API access issues
- Ensure users have the required attributes (email, name, etc.) populated
- Try a manual sync to see if specific error messages appear
Support Resources
Need help with your Google Workspace integration?- Google Documentation: Review Google Workspace Admin SDK documentation for API reference
- June Support: Contact support for integration-specific assistance
- Community Forum: Join discussions about identity provider integrations
Syncing data from Google Workspace to June may take up to 15 minutes based on the number of users in your Google Workspace environment.